Antispam
Included Antispam
With the antispam tools included with every Smardove license, email administrators can achieve immediate spam prevention simply by managing:
SpamAssassin-based Pattern Matching
rSpamd support
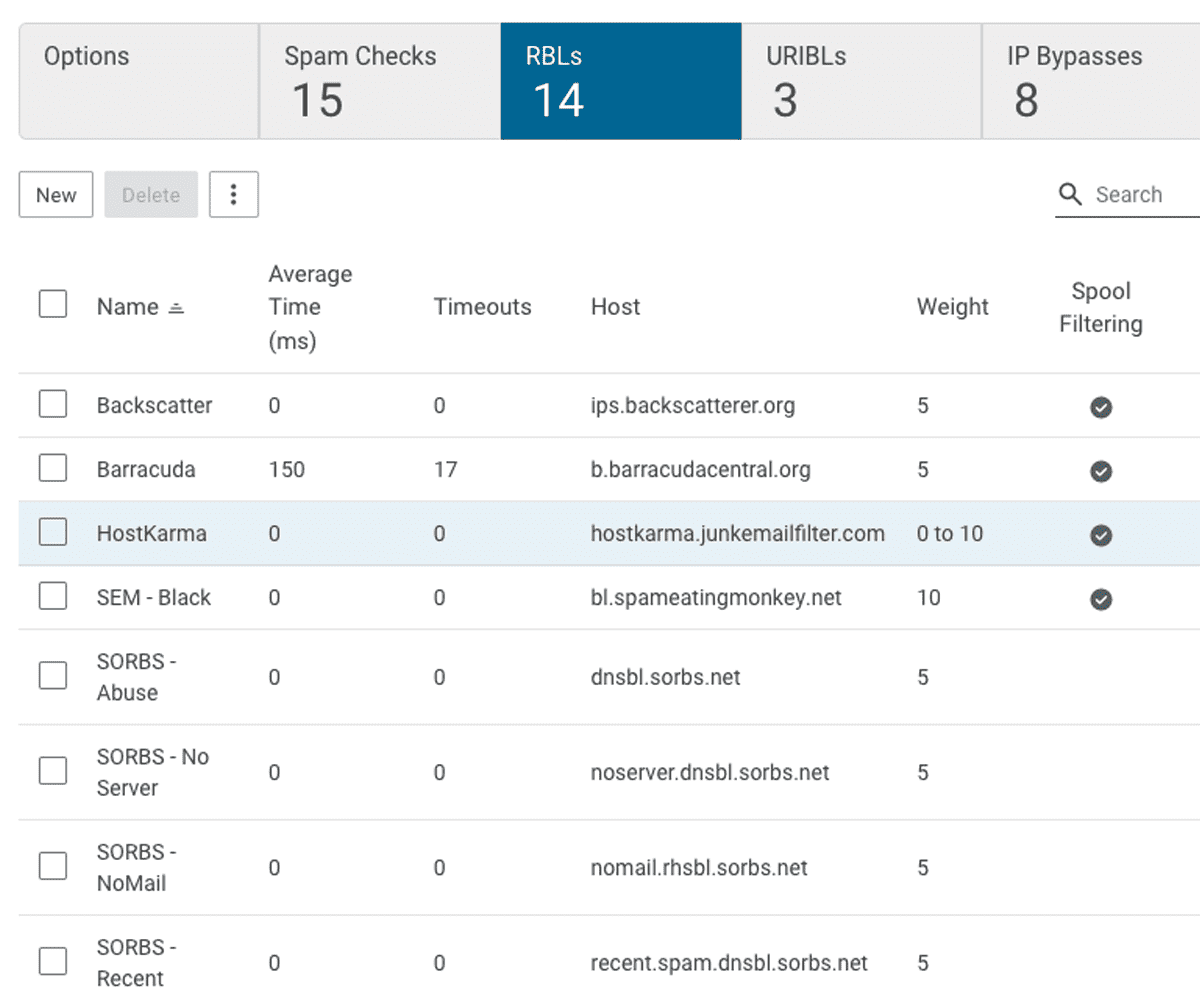
Pre-configured URIBLs and RBLs, by default
The ability to add custom URIBLs and RBLs
Greylisting, DMARC, DKIM and SPF
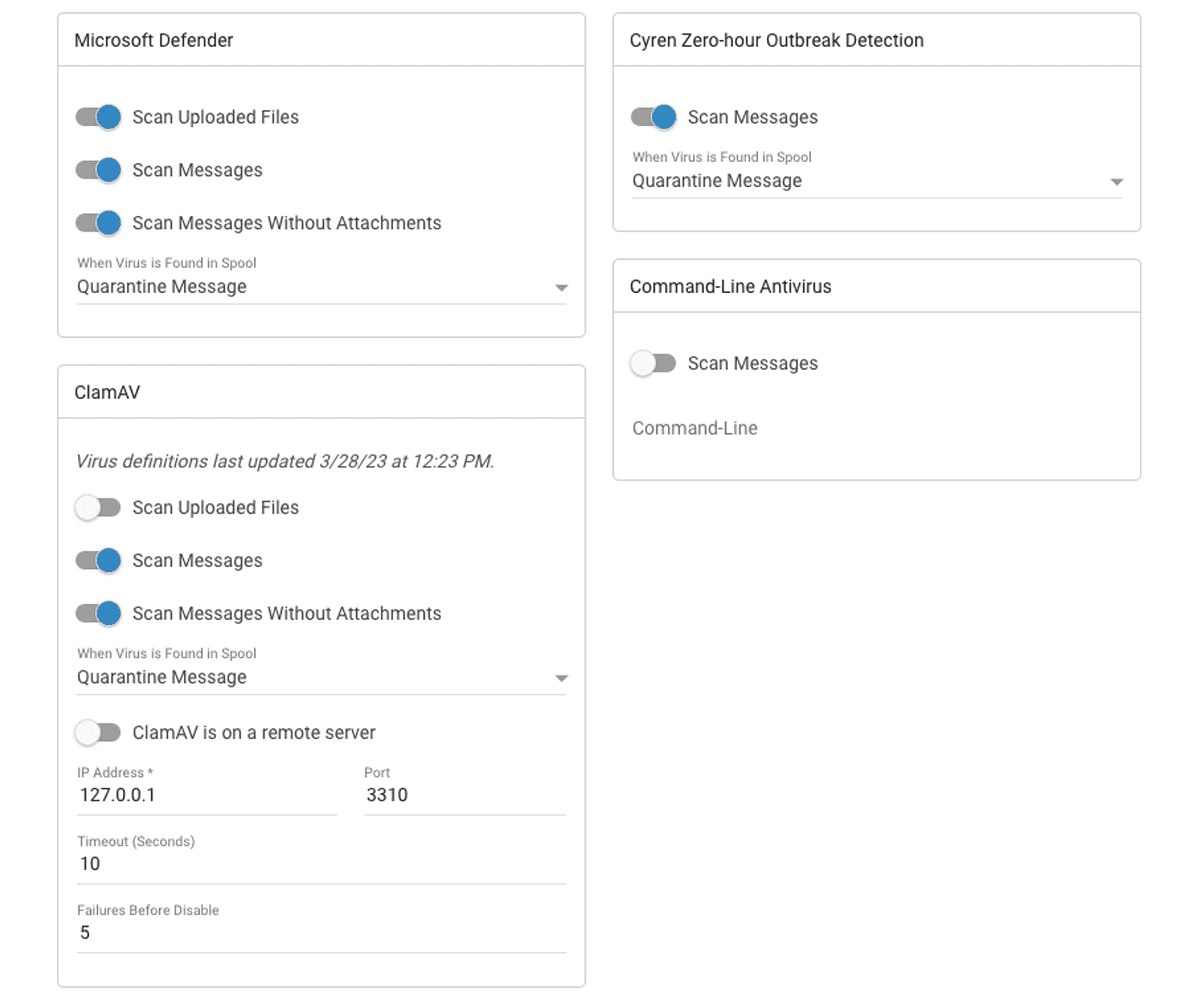
Integration with third-party products and services